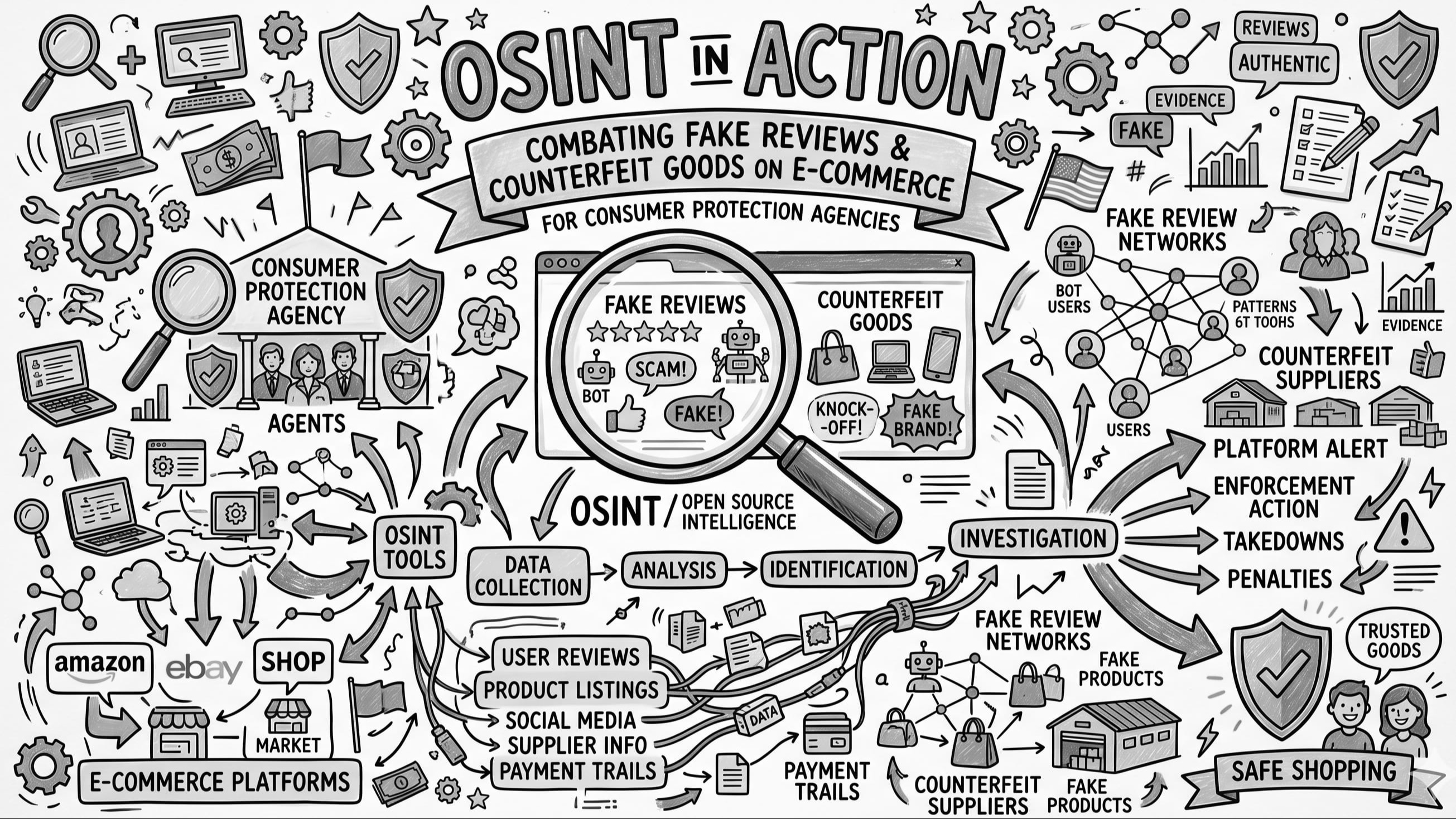
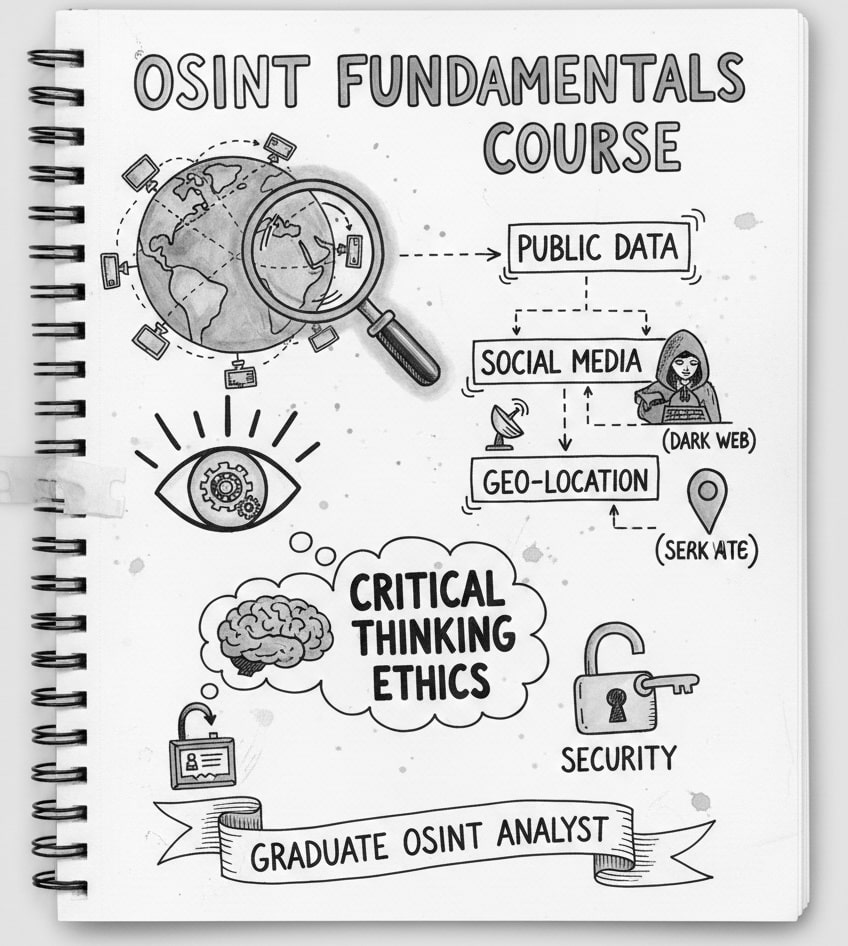
The explosive growth of e-commerce has created unprecedented opportunities for consumers — but also for fraudsters. Fake product reviews, counterfeit goods, and deceptive seller practices have become endemic across major online marketplaces. For consumer protection agencies, Open Source Intelligence (OSINT) offers a powerful, cost-effective toolkit to detect, investigate, and act against these violations — without requiring covert operations or judicial warrants for initial evidence gathering.
Understanding the Scale of E-Commerce Fraud
Counterfeit goods and fake reviews are no longer isolated incidents. They represent an organised, transnational threat operating at a scale that traditional enforcement methods simply cannot match.
- Fake reviews are often generated by coordinated networks — sometimes involving thousands of paid reviewers — to artificially inflate product ratings and deceive buyers.
- Counterfeit goods ranging from luxury items and electronics to pharmaceuticals and safety equipment are listed alongside genuine products, often indistinguishable to the average consumer.
- Sellers frequently operate across multiple platforms simultaneously, using shell identities to evade detection and reinstate banned accounts.
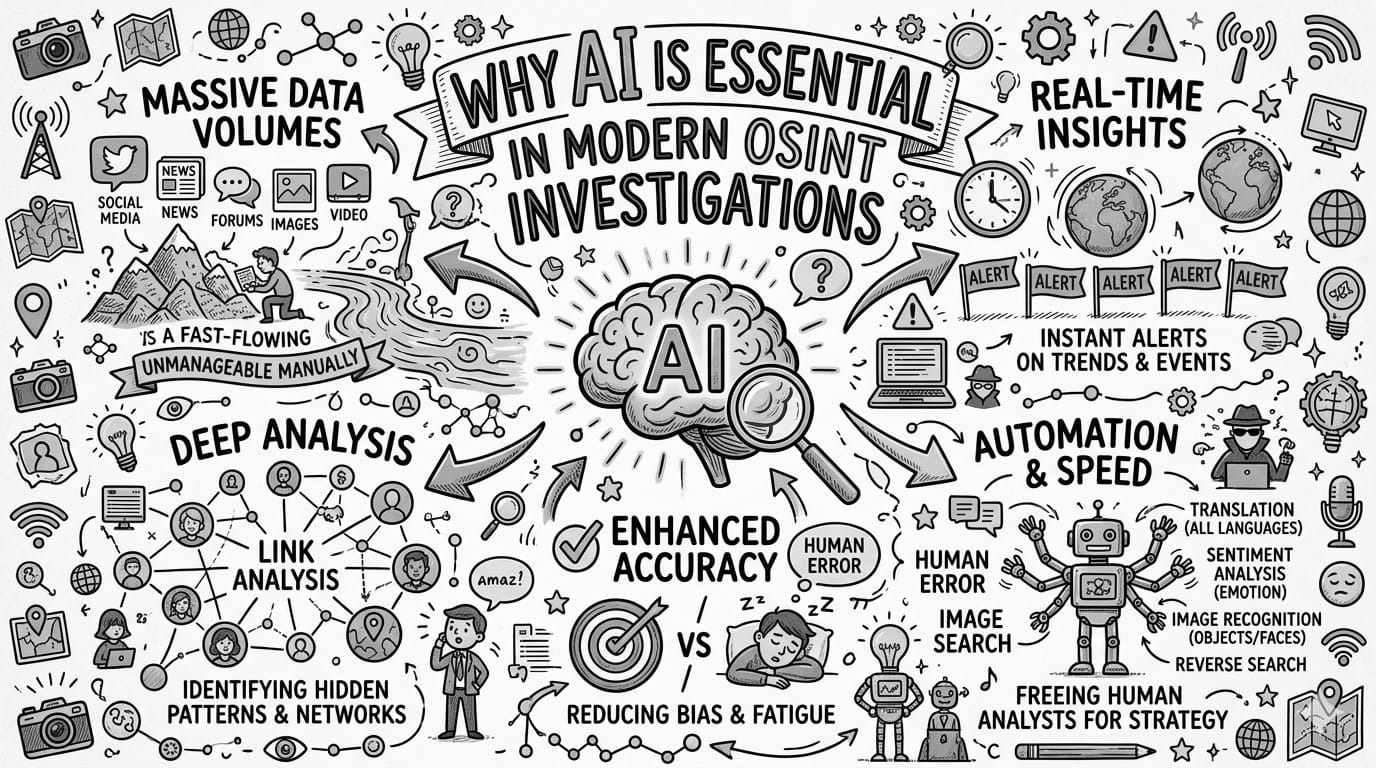
Traditional enforcement methods — consumer complaints, physical inspections, and tip-offs — are too slow and too narrow in scope to address the volume and velocity of online fraud. OSINT changes the calculus.
The OSINT Approach
Consumer protection agencies can deploy a layered OSINT strategy combining multiple open data sources and analytical techniques across four primary investigative tracks.
Review Pattern Analysis
- A sudden spike in 5-star reviews within a short time window following a product listing
- Reviewers with no prior purchase history or who have reviewed hundreds of unrelated products
- Identical or near-identical review text appearing across different products or sellers
- Clusters of reviews originating from the same geographic region or posted at the same time of day
- Public review data from Amazon, Lazada, Shopee, Tokopedia, and similar platforms
- Third-party review audit tools such as Fakespot or ReviewMeta (publicly accessible)
- Natural Language Processing (NLP) to detect templated or AI-generated review language
- Social media groups and Telegram channels where paid review schemes are openly advertised
An agency analyst notices a newly listed electronics brand achieving a 4.9-star rating with over 2,000 reviews within 30 days of launch. Cross-referencing reviewer profiles reveals many have reviewed 50+ products across unrelated categories in the same month. A search on Facebook groups uncovers a recruitment post offering payment in exchange for verified purchases and 5-star reviews on the exact platform in question. This forms the basis of a formal investigation.
Counterfeit Goods Detection
- Products listed at prices dramatically below authentic market value
- Seller accounts using brand logos, trademarked names, or imagery without authorisation
- Product photos that are slightly altered versions of official brand images
- Seller registration details pointing to known counterfeit supply hubs
- Reverse image search (Google Images, TinEye) to identify stolen or manipulated product photos
- WHOIS lookups and domain registration data to trace seller websites
- Business registry databases to verify legitimate import or distribution licences
- Brand protection databases and trademark registries (publicly available in many jurisdictions)
- Cross-platform searches to identify the same seller operating under different names
An analyst receives a tip about counterfeit luxury handbags being sold on multiple platforms. Using reverse image search, they confirm that product photos are stolen from the official brand website with slight colour modifications. WHOIS data on the seller's linked website reveals it was registered two weeks prior using a privacy shield service. The same product images are then found listed under seven different seller accounts across three platforms — all registered within the same week. Investigators flag all accounts and refer findings to the brand owner and platform operators for coordinated takedown.
Cross-Platform Seller Network Mapping
- The same seller operating across multiple platforms under different identities
- Shared phone numbers, email addresses, bank accounts, or delivery addresses across seller profiles
- Network clusters of sellers who mutually review each other's products (review rings)
- Open seller profile data from marketplace platforms
- Email and phone number lookup tools (where legally permissible)
- Social network analysis (SNA) tools to map relationships between accounts
- Public company registry data to identify shared directorships or registered addresses
A consumer protection agency maps a network of 40 seller accounts across Shopee, Lazada, and a local e-commerce platform. Despite using different names and profile photos, OSINT analysis reveals overlapping phone numbers and shared physical addresses in their seller registration data. Social network analysis shows these accounts collectively represent a coordinated counterfeit ring, with each account boosting the others' ratings through reciprocal reviews. The full network map is handed to law enforcement for simultaneous action.
Social Media Monitoring for Organised Fraud Schemes
- Public Telegram groups, Facebook groups, or forums openly recruiting fake reviewers
- Influencers or resellers promoting counterfeit goods while falsely claiming authenticity
- Advertisements targeting consumers with deceptive pricing or counterfeit luxury items
- Keyword monitoring on Telegram, Facebook, Reddit, and local forums
- Hashtag analysis on Instagram and TikTok for counterfeit product promotion
- Screenshot archiving tools to preserve evidence before content is deleted
- Geolocation metadata from publicly shared images to identify physical source locations
An analyst monitoring Telegram uncovers a public channel with over 15,000 members where administrators coordinate fake review campaigns. Members are instructed to purchase a product, submit a 5-star review, and send a screenshot to receive a cash refund via a payment app. The channel openly names the target platforms and products. Screenshots are archived as evidence, and the agency issues platform notifications while coordinating with payment processors to trace the refund flows.
From OSINT to Enforcement: The Evidence Pipeline
OSINT findings do not automatically constitute legal evidence, but they serve a critical function in the enforcement pipeline — from initial detection all the way through to policy reform.
| Stage | Role of OSINT | Output |
|---|---|---|
| Detection | Identifies suspicious patterns at scale across platforms | Signals |
| Prioritisation | Helps agencies focus limited resources on the highest-impact cases | Case list |
| Investigation Support | Provides leads, network maps, and preliminary evidence for formal inquiry | Intel package |
| Legal Referral | Packages findings for law enforcement or judicial action | Case file |
| Platform Engagement | Supports takedown requests to e-commerce operators | Takedown notice |
| Policy Advocacy | Provides data to support regulatory reform and platform accountability measures | Policy brief |
Challenges and Ethical Considerations
While OSINT is powerful, agencies must navigate several constraints to ensure investigations remain legally defensible and ethically grounded.
Conclusion
OSINT equips consumer protection agencies with the ability to operate at the speed and scale of modern e-commerce fraud. By systematically monitoring review patterns, tracing counterfeit seller networks, and mapping coordinated fraud schemes across platforms, agencies can shift from reactive enforcement to proactive market surveillance.
The result is a fairer, safer digital marketplace for consumers and legitimate businesses alike — built not on extraordinary surveillance powers, but on the disciplined, lawful analysis of information that bad actors have already made public.
This article is part of a series exploring the application of Open Source Intelligence across government agencies.