How to Investigate Social Media Accounts Using Open Source Intelligence
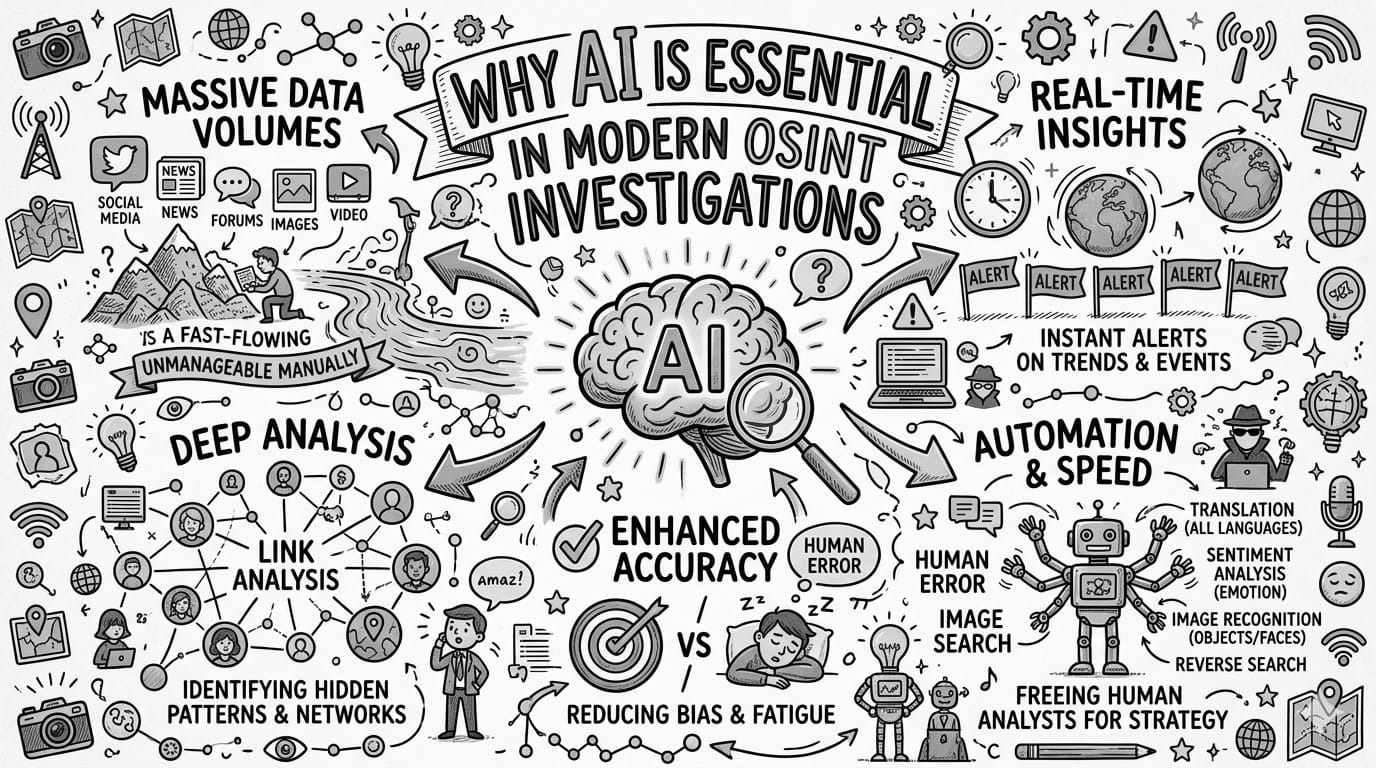
Social media platforms hold vast quantities of open-source intelligence. For investigators, compliance professionals, and security teams, the ability to systematically query, cross-reference, and analyse social profiles, networks, and activity data is an essential capability in any modern OSINT workflow.
Why Social Media is Central to OSINT Investigations
Individuals and organisations leave persistent, publicly accessible digital trails across social media platforms. LinkedIn reveals professional histories, connections, and organisational affiliations. Twitter/X surfaces opinions, associations, and real-time activity. Instagram and Facebook expose geographic patterns, social circles, and lifestyle indicators. YouTube channels can reveal ideological positions, technical knowledge, or operational activities.
Unlike corporate registries or court records — which capture declared facts — social media captures behaviour. It shows who a subject associates with, how they present themselves publicly, and what they claim to do. Crucially, it frequently reveals contradictions: a subject who claims to be based in Singapore but whose posts are consistently geotagged in Dubai; a company director who claims no knowledge of an organisation but who follows all its key members on LinkedIn.
"The challenge in social media OSINT is not the absence of information — it is the volume. Systematic, tool-supported methodology is the only way to extract signal from noise at investigation scale."
This guide presents a complete methodology for conducting social media investigations using OSINT techniques, structured around the capabilities of the NexVision OSINT360 platform — which integrates multi-platform social search, profile analysis, network mapping, and follower/connection intelligence in a single environment.
NexVision OSINT360 — Social Intelligence Module
The NexVision Social module provides investigators with unified search and analysis across LinkedIn, Twitter/X, Instagram, YouTube, and Facebook — including profile overviews, connection graphs, follower/following lists, endorsement data, and post history — all without requiring a personal account on each platform.
Access the NexVision OSINT360 platform →Understanding the Investigation Scope
Before conducting any social media investigation, the analyst must define the scope precisely. Social media OSINT can be conducted to support a wide range of investigative objectives:
Subject profiling — building a comprehensive picture of an individual's online identity, associations, claimed affiliations, and activity patterns to support background checks, due diligence, or threat assessments.
Corporate investigations — identifying the real people behind an entity by tracing employee profiles, executive networks, and organisational connections declared on professional platforms.
Disinformation and influence operations — detecting coordinated inauthentic behaviour by analysing follower/following patterns, account age, activity synchrony, and content amplification networks.
Fraud and impersonation — identifying fake accounts, cloned profiles, or synthetic personas used to deceive targets or manipulate public discourse.
Sanctions and PEP screening — identifying social media presence for persons of interest to establish current location, associations, or activities inconsistent with declared status.
Each objective shapes which platforms are prioritised, which data points are collected, and how findings are interpreted. Define this clearly before beginning.
The Investigation Methodology
Initial Subject Identification Across Platforms
Begin by searching for the subject — whether an individual or an organisation — across all major social media platforms simultaneously. Using the NexVision Social search functions, query the subject's full name, known usernames, email address prefixes, and any associated aliases across LinkedIn, Twitter/X, Instagram, Facebook, and YouTube.
The goal of this phase is not deep analysis but breadth: establish which platforms the subject is active on, which usernames are in use, and whether multiple accounts exist on the same platform. Note all account handles, profile URLs, and display names discovered. Cross-reference usernames across platforms — many individuals reuse the same handle, which allows rapid attribution of accounts across networks.
Red flag: A subject who appears active across many platforms under slightly different name variations — with no cross-linking between accounts — may be maintaining deliberately compartmentalised identities. This warrants closer scrutiny at later stages.
Platform-Specific Profile Overview
Once accounts have been identified, retrieve a full profile overview for each. The NexVision Social overview functions aggregate the key metadata from each platform: account creation date, follower/following counts, post volume and frequency, biographical information, linked URLs, location declarations, and profile image.
When reviewing profile data, pay close attention to inconsistencies between platforms. A LinkedIn profile claiming 20 years' experience in a senior sector, but a Twitter account created just 18 months ago with minimal followers, suggests either a newly created supplementary account or a potentially fabricated professional identity.
Connection and Network Analysis
LinkedIn connections represent a declared professional network — one of the richest open-source intelligence assets available for corporate investigations. Using the NexVision LinkedIn Connections function, retrieve and analyse the subject's visible connection graph.
Key analytical questions include: Does the subject have connections at the companies or organisations they claim to have worked for? Are senior executives of regulated entities connected to the subject despite denying knowledge of them? Does the connection network include known persons of interest, PEPs, or sanctioned individuals identified in earlier investigation steps?
Network analysis also supports organisational mapping. By identifying shared connections between the subject and other individuals under investigation, analysts can reconstruct informal professional relationships that do not appear in any corporate registry.
Watch for: Connection networks that are unusually small for the claimed career duration, or that consist predominantly of accounts from a single country inconsistent with the subject's claimed location, may indicate a synthetic or recently created professional profile.
Endorsement and Credential Verification
LinkedIn's endorsement system — where connections validate a subject's declared skills — provides a secondary verification signal that is frequently overlooked in OSINT investigations. The NexVision LinkedIn Endorsements function retrieves the endorsement data for a given profile.
Genuine professionals in established fields typically accumulate endorsements from former colleagues, clients, and industry peers who are identifiably real and active on the platform. A subject claiming expertise in a regulated domain — law, finance, medicine, engineering — but whose skill endorsements come exclusively from newly created accounts, geographically implausible connections, or individuals with no apparent professional relationship, presents a credibility concern.
Cross-reference key endorsers against the full investigation to determine whether they are genuine individuals or potentially part of the same constructed network.
Follower Analysis
The follower graphs of a social media account are among the most intelligence-rich datasets available through open sources. They reveal not just who considers the subject worth following — a signal of real-world reputation, affiliation, and influence — but also how the subject's audience is composed.
Using the NexVision Social followers functions, retrieve follower lists for the subject across Twitter/X, Instagram, and Facebook. Analyse the data at multiple levels:
Follower quality assessment: A high follower count composed predominantly of accounts with no profile images, zero posts, and recent creation dates is a strong indicator of purchased or inauthentic followers — a common feature of influence operations and reputation manipulation. Conversely, followers drawn from identifiable industry figures, journalists, and verified accounts carry a very different evidentiary weight.
Mutual connection mapping: Cross-referencing followers across multiple subjects under investigation frequently reveals shared network hubs — accounts that bridge otherwise apparently unconnected individuals and organisations.
Red flag: A Twitter account with 50,000 followers but a follower base composed almost entirely of accounts created within a short time window, with no profile images and zero engagement, exhibits the classic footprint of a coordinated follower inflation operation.
Post and Content History Analysis
A subject's post history is a chronological record of their public statements, associations, and activities. It frequently contradicts other claims made in formal filings or during due diligence processes, and can establish timelines that are forensically valuable in both compliance and legal contexts.
Using the NexVision LinkedIn Posts function — and complementing it with open web archival of Twitter/X, Instagram, and Facebook content — reconstruct the subject's visible content history. Key analytical objectives include:
Timeline verification: Does the subject's post history align with their declared professional chronology? Posts from a claimed period of employment at one company, made during business hours and referencing another employer's activities, create an evidentiary conflict that requires explanation.
Geolocation signals: Photos, tagged locations, check-ins, and contextual references within posts can place an individual in a specific location at a specific time. This is particularly relevant for subjects under travel restrictions, or who claim to reside in a jurisdiction inconsistent with their apparent activities.
Association disclosure: A subject may deny involvement with an organisation in formal documentation while simultaneously publishing posts praising that organisation's leadership, sharing its content, or tagging its accounts. Post history makes these associations discoverable.
Hard stop: Post content identifying a subject in proximity to sanctioned entities, criminal proceedings, or prohibited jurisdictions must be immediately escalated and preserved with full timestamp and URL documentation before any further investigation steps are taken.
Cross-Platform Correlation and Identity Attribution
Once data has been collected across all available platforms, the investigation enters its most analytically demanding phase: cross-platform correlation. The objective is to confirm that accounts identified across different networks belong to the same individual, and to identify additional accounts not yet discovered.
Correlation techniques available through open sources include: shared profile images (reverse image search via TinEye or Google Images), consistent biographical language, shared external URLs referenced in bios, identical or near-identical usernames, and overlapping posting timestamps that suggest a single user managing multiple accounts.
Where accounts cannot be directly attributed through content correlation, network analysis provides a complementary approach: if an unknown account follows the same unusual combination of accounts as a confirmed subject, the probability of common identity increases significantly.
Best practice: Document every attribution finding with its specific evidentiary basis. Stating that an account "appears to belong to" a subject without specifying which correlation technique produced that finding is insufficient for compliance or legal purposes.
Detecting Inauthentic Accounts and Coordinated Behaviour
Social media investigations increasingly require analysts to assess not just what accounts say, but whether they are genuine. Inauthentic accounts — including bots, sock puppets, and coordinated synthetic networks — are widely used in influence operations, corporate reputation manipulation, and sanctions evasion schemes designed to manufacture a false appearance of legitimacy.
Key indicators of inauthentic or coordinated behaviour include: account creation dates clustered within a short window; profile images that return results in reverse image search consistent with stock photography or AI generation; posting behaviour that is precisely timed and rhythmically regular in ways inconsistent with organic human activity; content that is largely reshared from a single source without original commentary; and follower networks that are mutually cross-connected in a closed loop.
When conducting due diligence on a corporate entity, the discovery that its claimed employee base consists primarily of inauthentic LinkedIn profiles — or that its social media following was manufactured rather than organically accumulated — is a significant finding that directly bears on the credibility of its claimed operations.
Red flag: A company claiming 500 employees on its website, but whose LinkedIn presence shows fewer than 10 verifiable employee profiles — all created within the past six months, with generic profile images and no meaningful work history — is exhibiting a cluster of indicators consistent with a paper entity.
Integrating Social Media Findings with Broader OSINT
Social media intelligence does not operate in isolation. The full value of the methodology described in this guide is realised when social media findings are systematically integrated with corporate registry data, sanctions screening results, court records, adverse media, and digital footprint analysis as part of a unified investigation workflow.
A LinkedIn profile declaring employment at a company is worth cross-referencing against that company's corporate filing data. A Twitter account referencing business activities in a sanctioned jurisdiction should trigger a renewed sanctions screening pass. A YouTube channel discussing technical capabilities in a regulated domain may require expert assessment to determine whether content constitutes a compliance concern.
The NexVision OSINT360 platform is designed precisely for this integration — providing a unified environment in which social intelligence from the NexVision Social module feeds directly into corporate, sanctions, and technical OSINT workflows, without the data silos that fragment investigations conducted across multiple disconnected tools.
Assigning a Risk Rating and Producing the Report
With the social media investigation complete, findings must be consolidated into a structured assessment with a defensible risk rating. As with all OSINT-based due diligence, every conclusion must be grounded in a specific, citable source — and the distinction between confirmed facts, strong indicators, and unverified leads must be explicit throughout the report.
| Rating | Social Media Criteria | Recommended Action |
|---|---|---|
| Consistent, credible profiles across platforms. Network aligned with declared professional history. No adverse associations identified. | Proceed with standard periodic monitoring. | |
| Some inconsistencies between platforms or between social data and formal declarations. Unexplained gaps in post history. Minor association concerns. | Proceed with enhanced due diligence and documented monitoring cadence. | |
| Material contradictions between social profiles and declared history. Inauthentic account indicators. Associations with persons or entities of concern. Geolocation inconsistencies. | Do not proceed without further verification. Escalate to compliance and legal. | |
| Confirmed association with sanctioned individuals or entities via social graph. Evidence of coordinated inauthentic behaviour serving prohibited purposes. Posts confirming prohibited activities or jurisdictions. | Hard stop. Escalate immediately. Consider regulatory reporting obligations. |
The final social media intelligence report should include: an executive summary with risk rating; a per-platform account inventory with profile URLs, creation dates, and key metrics; a network map of significant connections and associations; a summary of any adverse or inconsistent findings; and a full source appendix with screenshots, timestamps, and archive links. Screenshots should be taken immediately upon discovery — social media content can be deleted rapidly once a subject becomes aware of scrutiny.
Ethical and Legal Boundaries
Social media OSINT must operate entirely within the bounds of publicly available information. This means querying only data that is genuinely public — not circumventing privacy settings, not creating false accounts to access restricted content, and not using techniques that could constitute unauthorised access to computer systems under applicable law.
Investigators should be mindful of data protection obligations. Personal data gathered about individuals during social media investigation is subject to GDPR in the UK and EU, the PDPA in Singapore, and equivalent legislation in other jurisdictions. A lawful basis — typically legitimate interest, proportionate to the investigative purpose — must be documented, and data must be handled and retained in accordance with applicable requirements.
Finally, maintain a complete and auditable record of every source consulted and every step taken in the investigation. This documentation is essential if findings are ever challenged, disclosed to regulators, or relied upon in legal or disciplinary proceedings.